Conversation
7666
7666@comp.lain.la
@meso Mateus Batalha is a braindead Francisco lackey who can't fucking understand how to work support at a hosting company. I get reports and I handle them inside 24 hours, which is a lot better than what pedophile Zuckerberg and crew does, and yet I get shit for it. Usually if one makes it Francisco's way before I am able to get to it, they open a ticket with me and I let them know it's resolved. Not this time!
Also fuck the IWF, those assholes need to either cooperate with me on these reports (see previous blog post) or jump off a bridge. Since they're from the UK, I'd rather they did the latter.
Also fuck the IWF, those assholes need to either cooperate with me on these reports (see previous blog post) or jump off a bridge. Since they're from the UK, I'd rather they did the latter.
pistolero
p@fsebugoutzone.orgpistolero
p@fsebugoutzone.orgPhantasm
phnt@fluffytail.org
@p @7666 @dsm @meso You can't run an instance on his servers anyway after 2 years (tried), because the IO on slabs is shit and upgrading to bigger SSDs doesn't make sense since it's cheaper elsewhere.
frantech-pleroma-servers.png
frantech-pleroma-servers.png
7666
7666@comp.lain.la
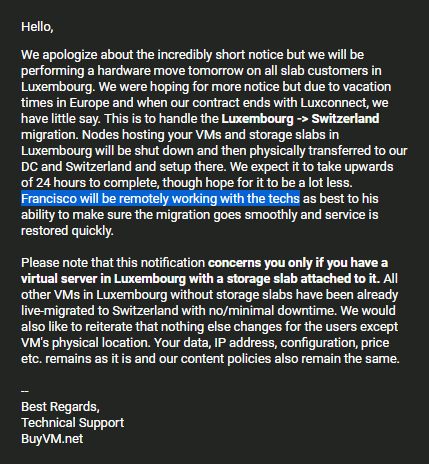
@p @dsm @meso It wasn't for loli, it was for a legitimate IWF CSAM report. I got that report at 2:18AM and one of my four edge nodes got zapped out of the blue at 4:47PM, so 14.5 hours after notification. My SLA is 24 hours or less though (and in 99% of cases it's less), but for today's case I would have had it fixed at about 6PM when I got off work and had the time to deal with today's reports.
7666
7666@comp.lain.la
@p @dsm @meso This was the first I saw of it (first image). No ticket. Nothing.
You know how I know it's the new owners? This was the courtesy I used to get previously (second image):
This is why I'm going to operate my own fucking hosting for this. HE already dropped us a 10Gbit line. I'm almost ready to start racking and provisioning. BuyVM just needs to keep their greasy fingers off the "deliberate fuckup" button a little while longer.
You know how I know it's the new owners? This was the courtesy I used to get previously (second image):
This is why I'm going to operate my own fucking hosting for this. HE already dropped us a 10Gbit line. I'm almost ready to start racking and provisioning. BuyVM just needs to keep their greasy fingers off the "deliberate fuckup" button a little while longer.
anime graf mays 🛰️🪐
graf@poa.st
@phnt @7666 @dsm @p @meso I remember reading on LET (this thread https://lowendtalk.com/discussion/201647/for-immediate... ) but I had no idea that it was completed. No email reached me for that but I did receive the notice about the move to Switzerland. And within 3 hours (maybe 2, it was late) that VPS was offline. It was only ever used as a storage server for europoor CDN edge nodes, but it's already failed over to another region in europe so I will take my time finding somewhere to relocate it. Sucks because Fran himself is great people, this is very poor service incl. OP if it's true he didn't have 24hr to respond
pistolero
p@fsebugoutzone.org👺 奇诺[流浪者]👹
adiz@mtl.jinxian.casa@p @7666 @dsm @meso For what it's worth, we provide hosting at scale. From VMs to full dedicated servers. https://prometheus.systems
7666
7666@comp.lain.la
@dcc @phnt @dsm @p @meso @graf I know we've talked in the past but you can still run your hosting business out of our DC if you want to make things move faster.
Colo has been way more profitable than VMs right now, I'm just waiting to get that last bit of transit in so we have the holy trifecta of DIA, transit, and IX peering and then I don't have to ever worry about network bandwidth ever again.
There's also the four racks in my basement available for "basement" prices lmao, just that the fiber line I got tunneled into the property is 500/500 only.
Colo has been way more profitable than VMs right now, I'm just waiting to get that last bit of transit in so we have the holy trifecta of DIA, transit, and IX peering and then I don't have to ever worry about network bandwidth ever again.
There's also the four racks in my basement available for "basement" prices lmao, just that the fiber line I got tunneled into the property is 500/500 only.
✙ dcc 

dcc@annihilation.social
@7666 @phnt @dsm @p @meso @graf The hosting is not the issues, the issue for me is the llc and i have to wait for some shit to happen before i can start it. Also if i get fiber any time soon it better for than to be done before i start hosting peoples stuff. ( I also want to add ac  )
)
IMG_20250628_154328.png
 )
)IMG_20250628_154328.png
7666
7666@comp.lain.la
@dsm @dcc @phnt @p @meso @graf It's not "Jade's" ToS, it's ToS for all services and I've approved the language myself (otherwise I would be a big fat hypocrite hosting my shit on the same network and not being subject to the same provisions).
Outside of "no Tor" (we're just not equipped to handle the heat from this yet) and general "don't break US law" clauses, you'll find it very permissive and deliberately open ended.
https://nulled.llc/terms-of-service
Outside of "no Tor" (we're just not equipped to handle the heat from this yet) and general "don't break US law" clauses, you'll find it very permissive and deliberately open ended.
https://nulled.llc/terms-of-service
7666
7666@comp.lain.la
@meso This should now be resolved, although it might run like shit for the next hour or so as the cache rebuilds.
arcana@layer02.net
arcana@layer02.net7666
7666@comp.lain.la
@p @dcc @phnt @dsm @meso @graf "Without authorization" is the key phrase there. I don't mean "Without your target's authorization", I mean "without OUR authorization". Aka open a ticket with a valid use case and ask away.
The reason for this is back in my days working for Linode we'd tag security researcher accounts internally, so when the inevitable pissed off mid-40's sysadmin came knocking after Kevin Mitnick's company banged up their leaky vulnerable IIS 6 servers we'd have a canned response ready to go, and we could validate it wasn't ACTUALLY some asshole using us as their fancy new C2 instance for a botnet or whatever.
(Yes, KnowBe4 was a huge Linode customer circa 2016. It's been almost a decade, I'm sure I can divulge that now, and they're probably sucking AWS cock now anyway.)
(I also remember when that Finnish fuck zeekill/ryan spammed Chris Aker's SSN all over IRC after busting into their "private" OFTC channel. That was funny.)
The reason for this is back in my days working for Linode we'd tag security researcher accounts internally, so when the inevitable pissed off mid-40's sysadmin came knocking after Kevin Mitnick's company banged up their leaky vulnerable IIS 6 servers we'd have a canned response ready to go, and we could validate it wasn't ACTUALLY some asshole using us as their fancy new C2 instance for a botnet or whatever.
(Yes, KnowBe4 was a huge Linode customer circa 2016. It's been almost a decade, I'm sure I can divulge that now, and they're probably sucking AWS cock now anyway.)
(I also remember when that Finnish fuck zeekill/ryan spammed Chris Aker's SSN all over IRC after busting into their "private" OFTC channel. That was funny.)
pistolero
p@fsebugoutzone.org🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @dcc @7666 @phnt @dsm @meso @graf @mint
magnet:?xt=urn:btih:3E9A688EA2BCFA8F1EC76010DF2AA802485779D4&dn=%5BExiled-Destiny%5D+Armitage+III+%5BDVD+Dual-audio%5D&tr=http%3A%2F%2Fnyaa.tracker.wf%3A7777%2Fannounce&tr=udp%3A%2F%2Fopen.stealth.si%3A80%2Fannounce&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.coppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=http%3A%2F%2Ftracker.openbittorrent.com%3A80%2Fannounce&tr=udp%3A%2F%2Fopentracker.i2p.rocks%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.internetwarriors.net%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Fcoppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.zer0day.to%3A1337%2Fannounce
magnet:?xt=urn:btih:3E9A688EA2BCFA8F1EC76010DF2AA802485779D4&dn=%5BExiled-Destiny%5D+Armitage+III+%5BDVD+Dual-audio%5D&tr=http%3A%2F%2Fnyaa.tracker.wf%3A7777%2Fannounce&tr=udp%3A%2F%2Fopen.stealth.si%3A80%2Fannounce&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.coppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=http%3A%2F%2Ftracker.openbittorrent.com%3A80%2Fannounce&tr=udp%3A%2F%2Fopentracker.i2p.rocks%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.internetwarriors.net%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Fcoppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.zer0day.to%3A1337%2Fannounce
✙ dcc 

dcc@annihilation.social
@ins0mniak @7666 @phnt @dsm @p @meso @graf @mint Take mde extreme peace btw https://annihilation.social/media/up/extreampeace.tar.gz
✙ dcc 

dcc@annihilation.social
pistolero
p@fsebugoutzone.orgpistolero
p@fsebugoutzone.orgpistolero
p@fsebugoutzone.orgpistolero
p@fsebugoutzone.org
@ins0mniak @stelo @7666 @dcc @dsm @graf @meso @mint @phnt @sicp
> I also like to sleep with the tv on.
I do that, but I do something like Newsradio or Malcolm in the Middle or Space Ghost or Avenue 5 or King of the Hill or Futurama or Venture Brothers or whatever. Something that I've seen a million times so that it won't keep me up. (Only problem is the King of the Hill intro music is too loud; sometimes actually wakes me up. Tried include Seinfeld, the anxious whining actually kept me from falling asleep.)
I actually have a script for that; it takes a timeout and a list of directories, then it grabs the filenames, shuffles them, feeds them to mplayer, and kills mplayer after the timeout. So I turn that on, it'll run for two and a half hours and then stop; I'll be out by the then.
> I also like to sleep with the tv on.
I do that, but I do something like Newsradio or Malcolm in the Middle or Space Ghost or Avenue 5 or King of the Hill or Futurama or Venture Brothers or whatever. Something that I've seen a million times so that it won't keep me up. (Only problem is the King of the Hill intro music is too loud; sometimes actually wakes me up. Tried include Seinfeld, the anxious whining actually kept me from falling asleep.)
I actually have a script for that; it takes a timeout and a list of directories, then it grabs the filenames, shuffles them, feeds them to mplayer, and kills mplayer after the timeout. So I turn that on, it'll run for two and a half hours and then stop; I'll be out by the then.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @dcc @7666 @phnt @dsm @sicp @stelo @meso @graf @mint I like informercials and like...shitty trash tv. Spinger and Maury usually.
Ive downloaded so much crazy shit from ancient cable access that I can put it on my kodi and let it go all night. Mix it up with some anime or some b-horror.
gives some wicked cool dreams.
Ive downloaded so much crazy shit from ancient cable access that I can put it on my kodi and let it go all night. Mix it up with some anime or some b-horror.
gives some wicked cool dreams.
di0nysius the patomskyite
dsm@fsebugoutzone.orgpistolero
p@fsebugoutzone.orghorntoise
koropokkur@eveningzoo.club
havent heard much about soros buting radio stations since the USAID got shut down, either.
guaranteed that jew fucker was using our tax dollars to undermine our government. they were funding media matters, as well, id wager.
guaranteed that jew fucker was using our tax dollars to undermine our government. they were funding media matters, as well, id wager.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloudhorntoise
koropokkur@eveningzoo.club
i scroll up for titties or bebe saying "oh, she is very cute"
thats about it.
thats about it.
Clint Eastwood
Leyonhjelm@shitposter.worldanime graf mays 🛰️🪐
graf@poa.st
@ins0mniak @Leyonhjelm @dcc @7666 @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint Post moar Michelle Trachtenberg
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloudhorntoise
koropokkur@eveningzoo.club
that illness hit her hard... loks like shes over 50 in this pic
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
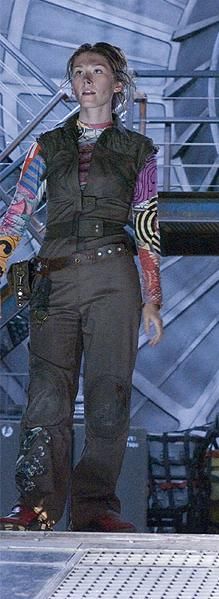
@fknretardlol @dcc @7666 @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm chick from eurotrip
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloudpistolero
p@fsebugoutzone.org
@koropokkur @dsm @dcc @7666 @phnt @sicp @stelo @ins0mniak @meso @graf @mint That was covered.
soros-usaid.jpg
soros-usaid.jpg
pistolero
p@fsebugoutzone.orgpistolero
p@fsebugoutzone.orghorntoise
koropokkur@eveningzoo.club
honestly, if the bondi doj doesnt charge him and the assholes who gave him the $$$ immediately, there is no law
di0nysius the patomskyite
dsm@fsebugoutzone.orgpistolero
p@fsebugoutzone.org
@ins0mniak @fknretardlol @7666 @Leyonhjelm @dcc @dsm @graf @koropokkur @meso @mint @phnt @sicp @stelo Wait, shit, this one?
hitchflash.gif
hitchflash.gif
pistolero
p@fsebugoutzone.org
@fknretardlol @ins0mniak @dcc @7666 @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm More relevant, she was the neighbor girl from The Adventures of Pete and Pete.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm yeah man
pistolero
p@fsebugoutzone.org
@koropokkur @dcc @7666 @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
> honestly, if the bondi doj doesnt charge him and the assholes who gave him the $$$ immediately, there is no law
I have some bad news for you about whether or not the swamp is actually going to be drained.
somebodys_doing_the_raping.png
> honestly, if the bondi doj doesnt charge him and the assholes who gave him the $$$ immediately, there is no law
I have some bad news for you about whether or not the swamp is actually going to be drained.
somebodys_doing_the_raping.png
Clint Eastwood
Leyonhjelm@shitposter.world
@p
I admire her positive attitude
@dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
I admire her positive attitude
@dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloudpistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Leyonhjelm @dcc @dsm @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo See, if @Godsend had said "The girl pulling her tits out in that gif you have and also the neighbor girl from Pete and Pete" then I would probably not have said "I don't know who that chick is and I don't care", but instead he talked about Buffy the Vampire Slayer, which I didn't watch because am not a teenage girl trying to rationalize being attracted to men while simultaneously viewing them as disgusting and violently predatory.
anime graf mays 🛰️🪐
graf@poa.st
@ins0mniak @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @Leyonhjelm They blurred out the logo on her shirt but not her tits. This is the most 2020s gif I've ever seen tbh
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo I don't know why her shirt is blurred out but I would definitely slow down long enough to take a photograph.
anime graf mays 🛰️🪐
graf@poa.st
@Leyonhjelm @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint Alyson Hannigan could have got it back then brother HH
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm I refuse to watch anything Joss Whedon does.
That firefly show looked dumb as shit
That firefly show looked dumb as shit
pistolero
p@fsebugoutzone.org
@graf @ins0mniak @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @mint @Leyonhjelm
> This is the most 2020s gif I've ever seen tbh
Timestamp on the file is 2007-03-22.
> This is the most 2020s gif I've ever seen tbh
Timestamp on the file is 2007-03-22.
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo Wow, she looks like shit in that image.
anime graf mays 🛰️🪐
graf@poa.st
@p @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm Brother that's even worse, also check IRC for a lmfao moment
 Shinji Stancil
Shinji Stancil 

TeaTootler@poa.st
@graf @ins0mniak @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @Leyonhjelm Uoh such nice perfect titties
Clint Eastwood
Leyonhjelm@shitposter.world
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
Clearly she needs a spanking
Clearly she needs a spanking
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo Apparently this was a completely different chick.
Clint Eastwood
Leyonhjelm@shitposter.world
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint yes it’s Allyson hannigan and is from Buffy
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo I am a man, I did not watch that show.
Clint Eastwood
Leyonhjelm@shitposter.world
@p @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo
She is better known for putting a flute in her pussy
She is better known for putting a flute in her pussy
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo ...Not impressive unless she *played* the flute.
Clint Eastwood
Leyonhjelm@shitposter.world
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
I don’t even know where most of my gifs come from. I’m surprised I know this one’s source
I don’t even know where most of my gifs come from. I’m surprised I know this one’s source
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo I'm surprised it ain't got teats in it.
I can't remember what I named the image of the statue squeezing her boobs at a monk, this one will have to do:
baby-statue.jpg
I can't remember what I named the image of the statue squeezing her boobs at a monk, this one will have to do:
baby-statue.jpg
Clint Eastwood
Leyonhjelm@shitposter.world
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
I wouldn’t know. I only saw the trailer for American Pie.
I wouldn’t know. I only saw the trailer for American Pie.
Clint Eastwood
Leyonhjelm@shitposter.world
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint
The miracle is known as “the lactation of St Bernard”
Truly Mary is the greatest mother
The miracle is known as “the lactation of St Bernard”
Truly Mary is the greatest mother
pistolero
p@fsebugoutzone.org
@SilverDeth Hey, you ever follow the wrong one around the grocery store?
pistolero
p@fsebugoutzone.org
@SilverDeth Ha, I was talking about that in the other thread. I've done that; woman was not surprised, apparently her friends had complained about that. (They had a group SMS where they'd ask each other questions about this kind of thing. "He's alone in his office and he just farted really loudly and then started cackling to himself." "MINE DOES THAT TOO")
di0nysius the patomskyite
dsm@fsebugoutzone.org
@p @ins0mniak @7666 @Godsend @Leyonhjelm @dcc @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo
I had a girlfriend pull that shit with Pink Floyd, "Yeah, you were a 15 year old boy once."
Ok, daddy issues, let's get analytical.
I had a girlfriend pull that shit with Pink Floyd, "Yeah, you were a 15 year old boy once."
Ok, daddy issues, let's get analytical.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@dsm @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @p @sicp @stelo @meso @graf @mint @Leyonhjelm That Buffy show sucked.
Clint Eastwood
Leyonhjelm@shitposter.world
@dsm
> Yeah, you were a 15 year old boy once
Still am on some level. All you have to do is get your tits out for this argument to end.
See how I brought this full circle? Everything always comes back to breasts.
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @p @sicp @stelo @ins0mniak @meso @graf @mint
> Yeah, you were a 15 year old boy once
Still am on some level. All you have to do is get your tits out for this argument to end.
See how I brought this full circle? Everything always comes back to breasts.
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @p @sicp @stelo @ins0mniak @meso @graf @mint
di0nysius the patomskyite
dsm@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @dcc @fknretardlol @graf @koropokkur @meso @mint @p @phnt @sicp @stelo
The Angel sex scene is why women wear niqabs in some parts of the world.
The Angel sex scene is why women wear niqabs in some parts of the world.
Clint Eastwood
Leyonhjelm@shitposter.world
@dsm
I saw Dogma. I know angels are ill-equipped.
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @p @sicp @stelo @ins0mniak @meso @graf @mint
I saw Dogma. I know angels are ill-equipped.
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @p @sicp @stelo @ins0mniak @meso @graf @mint
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@Leyonhjelm @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint I hate Kevin Smith stuff too.
Khanikken is James Khond
Chzikken_1486@poa.st
@ins0mniak @Leyonhjelm @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint I'll be in my bunk
Clint Eastwood
Leyonhjelm@shitposter.world
Edited 7 months ago
@ins0mniak
I hate the vast majority of Western media, but I've seen a lot of shit I didn't get to pick
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint
I hate the vast majority of Western media, but I've seen a lot of shit I didn't get to pick
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@Leyonhjelm @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint That Clerks movie was on the other day. I;ll never get the 90s thing of "oh man Im such a loser"
find something to do you know?
find something to do you know?
di0nysius the patomskyite
dsm@fsebugoutzone.org
@ins0mniak @Leyonhjelm @7666 @Godsend @dcc @fknretardlol @graf @koropokkur @meso @mint @p @phnt @sicp @stelo
It was historically relevant to show @f0x source for "do you want to making fuck berserker."
It was historically relevant to show @f0x source for "do you want to making fuck berserker."
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@dsm @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @p @sicp @stelo @meso @graf @mint @Leyonhjelm I was also the guy who made fun of people for crying over kurt cobain so that probably should be considered in my estimation of 90s era media
Godsend
Godsend@annihilation.social
@ins0mniak firefly was pretty good @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm
horntoise
koropokkur@eveningzoo.club
no one can convince me that his whore of a wife didnt have him murdered. then the cunt stole all the songs he was writing for his next album and performed them as her shitty band hole
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Meh theres something to that, I hated grunge tho man.
Shit is just depressing. Like idk why but I hear it and it just angers me.
Shit is just depressing. Like idk why but I hear it and it just angers me.
Clint Eastwood
Leyonhjelm@shitposter.world
@koropokkur
If he did kill himself it was because he married her, not because he was a junkie
@Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint
If he did kill himself it was because he married her, not because he was a junkie
@Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm the movie was fine but I don't think Joss Whedon had anything to do with it.
I cannot stand that dude lol
I cannot stand that dude lol
horntoise
koropokkur@eveningzoo.club
yeah... he was gonna divorce that cunt and take custody of their daughter. he had cleaned himself up and she kept being a junkie.
vile cunt had him killed and then stole all his songs and money.
vile cunt had him killed and then stole all his songs and money.
Clint Eastwood
Leyonhjelm@shitposter.world
@koropokkur
The odds of more is the only reason I haven't muted it at this point
@dcc @7666 @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint
The odds of more is the only reason I haven't muted it at this point
@dcc @7666 @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloudhorntoise
koropokkur@eveningzoo.club
me too. i listened to it, we all did. couldnt escape the shit at the time. it really did ruin everything. metallica hasnt written a decent song since. chili peppers blood sugar sex magic was a big seller, but compared to their earlier stuff, it was just a sellout album.
primus, tool, infextious grooves... those types of bands were the only thing that saved the 90s for musicians who knew how to play their instruments.
primus, tool, infextious grooves... those types of bands were the only thing that saved the 90s for musicians who knew how to play their instruments.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm I just listened to like midi files and random mix tapes I made for the most part.
I was a weird kid tho, I thought all the grunge shit was terrible. I used to wear loud colorful shirts and such just to rebel against all the flannel lol
I was a weird kid tho, I thought all the grunge shit was terrible. I used to wear loud colorful shirts and such just to rebel against all the flannel lol
horntoise
koropokkur@eveningzoo.club
yeah. those fags couldnt ruin flannel for me. michigan man is raised in the flannels. that shit is ours.
still infuriates me that the hipster faggots ruined the fedora.
i had to stop wearing mine and went back to the lid.
still infuriates me that the hipster faggots ruined the fedora.
i had to stop wearing mine and went back to the lid.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm I love flannel too but that thing where everyone was wearing their oversized flannels everyday or tying it around there waist was clone behavior.
I had this really cool shirt with these dolphins all over it and I got shit for wearing it, like ohhh sorry I forget to check with the retards at school before I set up my wardrobe haha.
I had this really cool shirt with these dolphins all over it and I got shit for wearing it, like ohhh sorry I forget to check with the retards at school before I set up my wardrobe haha.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm fuck was he with that psycho bitch for anyway?
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Shes the worst....and all this went down BEFORE the plastic surgery
https://www.youtube.com/watch?v=FEdm_U8-Sdg&t=137s
https://www.youtube.com/watch?v=FEdm_U8-Sdg&t=137s
Clint Eastwood
Leyonhjelm@shitposter.world
@ins0mniak
i think he was just high and a latent cuckold who needed someone to cheat on him. He was something of a female supremacist from the sounds of it and advocated for all the faggy alphabet soup. Today I believe he'd have cut his dick off.
@Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint
i think he was just high and a latent cuckold who needed someone to cheat on him. He was something of a female supremacist from the sounds of it and advocated for all the faggy alphabet soup. Today I believe he'd have cut his dick off.
@Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint
fknretardlol
fknretardlol@decayable.ink
would NOT ..this thing or that other thing , madonka
vile nasty creatures
vile nasty creatures
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@Leyonhjelm @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint Yeah the dress wearing thing he did was weird.
idk, my idea of music back then was ripping quake soundtrack to a tap deck.
idk, my idea of music back then was ripping quake soundtrack to a tap deck.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm oh yeah im not a fan of her ass either haha.
that was a weird time man.
that was a weird time man.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm yeah idk man.
there wasnt much going on then that every jived with me, i used to watch the Real World kinda just to make fun of it. I remember more about that than anything for some messed up reason.
there wasnt much going on then that every jived with me, i used to watch the Real World kinda just to make fun of it. I remember more about that than anything for some messed up reason.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Ive been out there. Fuckin rain bro
fknretardlol
fknretardlol@decayable.ink
indeed .. and the marine layer fog bs.. lived there 3 years
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Its hardcore man, I will say I do like their dark beers and endless cofe shops.
I guess makes sense, shits comfy as hell when its dark out like that all the time.
I guess makes sense, shits comfy as hell when its dark out like that all the time.
Clint Eastwood
Leyonhjelm@shitposter.world
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint
> he wasnt a fag
> he wasnt a fag
horntoise
koropokkur@eveningzoo.club
lol... i had a silk narwhal print shirt that was teal and orange.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm thats pimpin man.
horntoise
koropokkur@eveningzoo.club
yeah... i still have that shirt, but im too fat for it atm.
one day
one day
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm yeah i gotta lay off the pizza and stuff myself
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm for real.
nothing worse than ending up having to be the walmart scooter driver
nothing worse than ending up having to be the walmart scooter driver
fknretardlol
fknretardlol@decayable.ink
im fucked enough to almost be that guy.. but not all that fat
horntoise
koropokkur@eveningzoo.club
im around 200 so not exactly huge but def not fitting into my 32-34 shorts.
need to get back between 165-170.
need to get back between 165-170.
fknretardlol
fknretardlol@decayable.ink
im around 230.. but always been stocky.
nowhere near as strong as i used to be though..
le sadness
nowhere near as strong as i used to be though..
le sadness
fknretardlol
fknretardlol@decayable.ink
at one time , was 265.. wore large shits , same in pants
horntoise
koropokkur@eveningzoo.club
yeah. when the 36 starts getting tight, its time to start riding the bike and doing situps.
fknretardlol
fknretardlol@decayable.ink
riding a bike would be great !
i have a killer Mongoose mtn bike frame.. just needs the parts ..wheels , cranks etc.
i have a killer Mongoose mtn bike frame.. just needs the parts ..wheels , cranks etc.
Godsend
Godsend@annihilation.social
@koropokkur
Jewel Staite - Canadian cutie.
Oh wait she is here in BC...
@dcc @7666 @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint @Leyonhjelm
image.png
Jewel Staite - Canadian cutie.
Oh wait she is here in BC...
@dcc @7666 @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @graf @mint @Leyonhjelm
image.png
horntoise
koropokkur@eveningzoo.club
shes aged well, but she was so fresh back then. still had pudgy cheeks and crooked teeth.
very fine example of a yaeba girl.
very fine example of a yaeba girl.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm yeah i gotta lose about 20lbs or so. I dont want that porky ass guy sticking out you know?
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Im tall but I can kind of hide it for a bit
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Those things are cool I used to have one.
pistolero
p@fsebugoutzone.org
@dsm @7666 @Godsend @Leyonhjelm @dcc @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo You want to see a woman get absolutely furious, say a true thing without thinking about it.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm I have adhd I do that constantly.
Godsend
Godsend@annihilation.social
@p
Works for me, angry women get me off
@dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint @Leyonhjelm
Works for me, angry women get me off
@dcc @7666 @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @graf @mint @Leyonhjelm
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Yeah I love getting chicks worked up,
pistolero
p@fsebugoutzone.org
@koropokkur @ins0mniak @dsm @Godsend @dcc @7666 @f0x @fknretardlol @phnt @sicp @stelo @meso @graf @mint @Leyonhjelm Clearly, while he was alive, he would never have helped his wife write a song; that sort of thing is impossible. I think playing songs he wrote is probably more callous opportunism.
pistolero
p@fsebugoutzone.org
@ins0mniak @koropokkur @7666 @Godsend @Leyonhjelm @dcc @dsm @f0x @fknretardlol @graf @meso @mint @phnt @sicp @stelo "Flannel goths".
pistolero
p@fsebugoutzone.org
@koropokkur @ins0mniak @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm
> metallica hasnt written a decent song since.
Or before.
> metallica hasnt written a decent song since.
Or before.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm I didn't like the guitar breaking.
I mean once in a minute ok, but like every time....stupid. Why would you kill a guitar?
I mean once in a minute ok, but like every time....stupid. Why would you kill a guitar?
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm Clone wear.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm Megadeth is a far superior band. Also that shit of suing kids over mp3 downloading is unforgivable.
f0x
f0x@darkdork.dev
@ins0mniak @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm nothing faggier than going "no you can't do that" over a fucking music file.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@f0x @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm No kidding, suing your own fucking fans over a song download?
Lars is a fuckin pussy and a bitch.
Lars is a fuckin pussy and a bitch.
f0x
f0x@darkdork.dev
@ins0mniak @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm i have one experience with a man named lars otherwise and this tracks. can we get a study on this?
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@f0x @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm I thought it was badass when Trent reznor got mad at his record label and went online and told his fans to download everything of his they could off torrent lol
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@f0x @Godsend @dcc @7666 @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Oh Im down man ha
pistolero
p@fsebugoutzone.org
@Leyonhjelm @fknretardlol @7666 @Godsend @dcc @dsm @f0x @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo It's hard to tell what a person does because of core beliefs and what they do just to piss off the Christian Coalition, but his idea of being edgy was to wear a dress and kiss a dude on Letterman. Bone-smuggling was the main social-issues shibboleth at the time, having displaced dolphins eating the ozone layer, so musicians got asked about that kind of thing, and I don't think there are a lot of professional musicians or heroin addicts that have extremely strenuous objections to it.
di0nysius the patomskyite
dsm@fsebugoutzone.org
@Godsend @p @7666 @Leyonhjelm @dcc @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo
Are we even the same species?
Are we even the same species?
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @meso @graf @mint @Leyonhjelm If you want to be a badass get a Raspberry Pi and a library card.
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@sicp @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @Leyonhjelm no lies told here
🦃 Ins0mniak 🦃
ins0mniak@mikoshidata.cloud
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @meso @graf @mint @Leyonhjelm Yeah i like NIN, not a big fan but I dug their stuff.
I loved the Quake thing I thought that was really cool
I loved the Quake thing I thought that was really cool
pistolero
p@fsebugoutzone.org
@Godsend @7666 @Leyonhjelm @dcc @dsm @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo I slide up and I start doing hip-thrusts while gesturing at my genitals and then when she asks what I'm doing, I say "My bacon beacon beckons."
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @dcc @dsm @f0x @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo The other thing was like...he'd buy a guitar for breaking.
pistolero
p@fsebugoutzone.org
@f0x @ins0mniak @7666 @Godsend @Leyonhjelm @dcc @dsm @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo It's a sign of not having talked to a regular human in so long that they didn't even know that before Napster, 99% of all the musical recordings on earth were TDK-D90 cassettes that were either recorded from the radio or copies six times removed from an original recording that someone paid money for.
10_airstream.mp3
10_airstream.mp3
pistolero
p@fsebugoutzone.org
@f0x @ins0mniak @7666 @Godsend @Leyonhjelm @dcc @dsm @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo I have a friend named Lars that is a cool guy but he also has a long-ass Nordic name so maybe it's just non-vikings named Lars.
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @dcc @dsm @f0x @fknretardlol @graf @koropokkur @meso @mint @phnt @sicp @stelo Hey. HEY! This is library.
✙ dcc 

dcc@annihilation.social
@Twig @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo Made a fake version*
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
It’s the best purrke version you could ever get….
It’s the best purrke version you could ever get….
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @graf @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
Pawful purrrrrke
Pawful purrrrrke
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Cat, it’s me, be on my side 💗
Cat, it’s me, be on my side 💗
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Got it, be on my side, fight!
Got it, be on my side, fight!
pistolero
p@fsebugoutzone.org
@NeoCat @7666 @Godsend @Leyonhjelm @Twig @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo What the fuck are you babbling about?
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
I can handle that, the pawrrific opponent is DCC!
I can handle that, the pawrrific opponent is DCC!
@Twig @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Unless you're on the side of Christ. Then we can't be on the same side. I have chosen.
Unless you're on the side of Christ. Then we can't be on the same side. I have chosen.
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Christ is always on my side!
Christ is always on my side!
@Leyonhjelm @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat
You misspelled it, Chyna….
You misspelled it, Chyna….
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
I know it, we have a short time, dismantle DCC!
I know it, we have a short time, dismantle DCC!
✙ dcc 

dcc@annihilation.social
@p @Godsend @Twig @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm The devil: we must kill him
devil_gates.gif
1686936206572988.png
devil_gates.gif
1686936206572988.png
pistolero
p@fsebugoutzone.org
@Leyonhjelm @7666 @Godsend @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo Is he a bot or something?
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @koropokkur @meso @mint @phnt @sicp @stelo Maybe you can't see that guy on your instance.
@dcc @p @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo
Purrfect, bring on, I shall scorch your butts!
Purrfect, bring on, I shall scorch your butts!
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
Where is your accomplice…. Jonny, it’s his expertise…, drinking?!
Where is your accomplice…. Jonny, it’s his expertise…, drinking?!
pistolero
p@fsebugoutzone.org
@NeoCat @Twig @7666 @Godsend @Leyonhjelm @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo Holy shit, you're that "gummynerds" guy.
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
He got the wrong religion….
He got the wrong religion….
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Gummy nerds? Not Purrnerds
Gummy nerds? Not Purrnerds
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
That one was to DCC, he is the babysitter of Jonny the drunkard!
That one was to DCC, he is the babysitter of Jonny the drunkard!
@Twig @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
I actually don't know anyone you're talking about. I just didn't want to look stupid. 🐑
I actually don't know anyone you're talking about. I just didn't want to look stupid. 🐑
@ins0mniak @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @NeoCat @Leyonhjelm
The problem is that he doesn’t believe, say, nature’s god, those people are willing to believe anything….
The problem is that he doesn’t believe, say, nature’s god, those people are willing to believe anything….
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
It’s okay, attack DCC😆😄❤️
It’s okay, attack DCC😆😄❤️
Dr. Coyote Owens, Conspiracy Therapist
Coyote@shitposter.world
@dcc @Godsend @Twig @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm China isn't an issue. Trump could go down in history as one of the most significant presidents in world history by simply offering/inviting any and all regions of china a fast track application to US statehood, the new "diversity of states" is not imperialism, and would give unbelievable sway in a highly populated region (the only way Imperialism stabilized it's flailing nations) to ...
Imagine, even the most "red necky, backwards ass" region of China, seat in senate just like Alabama and Florida, and ... military bases, hub for foreign trade in region... China is as "split" internally as Red/Blue US.. could you imagine ideological splits that have common borders? That'd change the pattern of history.
Greenland? Canada? No... ANYWHERE in China.
Imagine, even the most "red necky, backwards ass" region of China, seat in senate just like Alabama and Florida, and ... military bases, hub for foreign trade in region... China is as "split" internally as Red/Blue US.. could you imagine ideological splits that have common borders? That'd change the pattern of history.
Greenland? Canada? No... ANYWHERE in China.
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Profound ethical problems….
Profound ethical problems….
Dr. Coyote Owens, Conspiracy Therapist
Coyote@shitposter.world
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo The fucking horsie is fucking pretty motherfuckers ;-) The man may not have been white, but he was right.
Dr. Coyote Owens, Conspiracy Therapist
Coyote@shitposter.world
@7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
/me now opens thread... to see how out of fucking context that was in ... ? hellthread, na.. all good. fuck the topic.
/me now opens thread... to see how out of fucking context that was in ... ? hellthread, na.. all good. fuck the topic.
@Coyote @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Meanwhile Trump is handling The Tough Cookie …..
Meanwhile Trump is handling The Tough Cookie …..
pistolero
p@fsebugoutzone.org
@NeoCat @Twig @7666 @Godsend @Leyonhjelm @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo If you're not a spambot, then please speak up pretty quickly.
pistolero
p@fsebugoutzone.org
@Coyote @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo
> hellthread, na.. all good. fuck the topic.
This was not. Anyway, I'm the fuck out of here.
> hellthread, na.. all good. fuck the topic.
This was not. Anyway, I'm the fuck out of here.
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @koropokkur @meso @mint @phnt @sicp @stelo I don't know who the Enya chick is unless you mean Enya.
nicetrysoros.jpg
nicetrysoros.jpg
pistolero
p@fsebugoutzone.org
@NeoCat @7666 @Godsend @Leyonhjelm @Twig @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo Are you or are you not "gummynerds"?
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @koropokkur @meso @mint @phnt @sicp @stelo
> mm sail away enry haha
ultrademon--seapunk--01_chatroom_with_enya.mp3
> mm sail away enry haha
ultrademon--seapunk--01_chatroom_with_enya.mp3
pistolero
p@fsebugoutzone.org
@Coyote Sometimes a thread is still good even after the boomers that got banned from NAS come to shit on it.
pistolero
p@fsebugoutzone.org
@ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dcc @dsm @f0x @fknretardlol @koropokkur @meso @mint @phnt @sicp @stelo I gotta escape this thread.
@dcc @ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @koropokkur @meso @mint @p @phnt @sicp @stelo
Sounds like Ramones
Sounds like Ramones
@ins0mniak @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @NeoCat @Leyonhjelm
Better than Metallica
Better than Metallica
✙ dcc 

dcc@annihilation.social
@Twig @ins0mniak @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @koropokkur @meso @mint @p @phnt @sicp @stelo I have that right here
06_in_my_darkest_hour.flac
06_in_my_darkest_hour.flac
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
O no, it’s a stark torture….
O no, it’s a stark torture….
✙ dcc 

dcc@annihilation.social
@Twig @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo Its the cure smarty pants
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Too dull, for babies?
Too dull, for babies?
@ins0mniak @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @NeoCat @Leyonhjelm
You need Jonny…
You need Jonny…
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Wow, definitely sounds better than Alex…
Wow, definitely sounds better than Alex…
✙ dcc 

dcc@annihilation.social
@p @Godsend @Twig @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Coyote @Leyonhjelm HE KEEPS LEAVING WHEN ITS GETING GOOD
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Some scary codes?
Some scary codes?
@ins0mniak @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @NeoCat @Leyonhjelm
Apparently this one is stupid one…
Apparently this one is stupid one…
Dr. Coyote Owens, Conspiracy Therapist
Coyote@shitposter.world
@dcc @Godsend @Twig @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm P? there's good reasons... don't worry, you won't be disappointed.
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Stupid question, just shoot like a tough cookie
Stupid question, just shoot like a tough cookie
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Translation…
You could eliminate the problem of telemarketers by acting interested in the product, but then trying to turn the conversation into phone sex.
Translation…
You could eliminate the problem of telemarketers by acting interested in the product, but then trying to turn the conversation into phone sex.
@Twig @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
It's been swell. But, I think it's time to cut the cord. Take care.
It's been swell. But, I think it's time to cut the cord. Take care.
✙ dcc 

dcc@annihilation.social
@NeoCat @Godsend @Twig @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm Why are you posting a bible quote at me?
Мат TL;DF MacShane
bigmattoidchimpin@annihilation.social
@dcc @NeoCat @7666 @Godsend @Leyonhjelm @Twig @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo You better convert before it's too late, or he's going to send Jeezus the Egyptian Magician spells at you through the cell towers. Then he's going to look into his crystal ball, get more demon-pozzed, and drop diss tracks on you based on what he has remote viewed about you in his psychotically delusional imagination.
✙ dcc 

dcc@annihilation.social
@bigmattoidchimpin @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo I got a better one for ya
Hell 11.jpg
Hell 11.jpg
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
😆, your weaving skills is impressive…
I say this is HIS glorious Song, see these animals impopossible.., touch of Jesus!
ssstwitter.com_1754211610895.mp4
😆, your weaving skills is impressive…
I say this is HIS glorious Song, see these animals impopossible.., touch of Jesus!
ssstwitter.com_1754211610895.mp4
@NeoCat @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
O Baby don’t go, didn’t you see me singing and polite pig, chill chicken
, and parrot 🦜?
O Baby don’t go, didn’t you see me singing and polite pig, chill chicken
, and parrot 🦜?
Мат TL;DF MacShane
bigmattoidchimpin@annihilation.social
@dcc @7666 @Godsend @Leyonhjelm @NeoCat @Twig @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo I got an even better one for ya: I don't have to worry about it one bit.
To quote M.C. Hammer the Real G: I told you, homeboy, you can't touch this. Yeah, that's how we livin' and ya know you can't touch this.
image.png
To quote M.C. Hammer the Real G: I told you, homeboy, you can't touch this. Yeah, that's how we livin' and ya know you can't touch this.
image.png
@bigmattoidchimpin @dcc @7666 @Godsend @Leyonhjelm @NeoCat @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
MC Hammer / watermelon Crossack Popsicles, someone is about to break 😄
clideo_editor_5355a0d877b94c21a3d60b9999194268.mp4
MC Hammer / watermelon Crossack Popsicles, someone is about to break 😄
clideo_editor_5355a0d877b94c21a3d60b9999194268.mp4
di0nysius the patomskyite
dsm@fsebugoutzone.org
@NeoCat @dcc @7666 @Godsend @Leyonhjelm @Twig @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
I deserve better enemies that sad stupid cuck.
I deserve better enemies that sad stupid cuck.
di0nysius the patomskyite
dsm@fsebugoutzone.org
@NeoCat @p @7666 @Godsend @Leyonhjelm @Twig @dcc @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @phnt @sicp @stelo
And you were sober when you wrote this.
Christ is lord, but this isn't sane.
And you were sober when you wrote this.
Christ is lord, but this isn't sane.
@dsm @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
I think this one is pretty good and sober one, and Alex has too much gumption to tell the truth.
I think this one is pretty good and sober one, and Alex has too much gumption to tell the truth.
Мат TL;DF MacShane
bigmattoidchimpin@annihilation.social
@Twig @7666 @Godsend @Leyonhjelm @NeoCat @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo Inability to recognize any sarcasm whatsoever from an already broken weirdo who makes AI generated shit cat videos all day, yet doesn't even know what a Siberian cat is, continues.
fknretardlol
fknretardlol@decayable.ink
ok.. i hate on AI a lot .. but Twig is pretty fuckin great at it ..
that ones 🔥
that ones 🔥
@fknretardlol @Godsend @bigmattoidchimpin @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
I think you missed this one…😘💗
clideo_editor_5355a0d877b94c21a3d60b9999194268.mp4
I think you missed this one…😘💗
clideo_editor_5355a0d877b94c21a3d60b9999194268.mp4
Edited 7 months ago
@ins0mniak @Godsend @bigmattoidchimpin @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @meso @mint @NeoCat @Leyonhjelm
Walla walla news
Australia has banned machetes in the country.
video_1754282767260.mp4
Walla walla news
Australia has banned machetes in the country.
video_1754282767260.mp4
@p @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Find the perfect audio for this clip 👇
ssstwitter.com_1754200975795.mp4
Find the perfect audio for this clip 👇
ssstwitter.com_1754200975795.mp4
horntoise
koropokkur@eveningzoo.club
the bigfoot and yetiboo guy is making dogshit now.
a shame cuz it had so much potential
saw some gay ewok version a week or so back... faggot killed the golden goose by fiending for clicks.
a shame cuz it had so much potential
saw some gay ewok version a week or so back... faggot killed the golden goose by fiending for clicks.
@dcc @NeoCat @7666 @Godsend @Leyonhjelm @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
Such head, a babysitter has a head😆
Such head, a babysitter has a head😆
Godsend
Godsend@annihilation.social
Kek, I didn't know they made Ye nerf his song.
Oh well, until we start owning our own banks, it be like that:
https://www.youtube.com/watch?v=YNlD2-ycQjQ - Nigga Hallelujah (no joke).
@Twig @koropokkur @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @meso @mint @p @phnt @sicp @stelo
Oh well, until we start owning our own banks, it be like that:
https://www.youtube.com/watch?v=YNlD2-ycQjQ - Nigga Hallelujah (no joke).
@Twig @koropokkur @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @meso @mint @p @phnt @sicp @stelo
Godsend
Godsend@annihilation.social
@DiamondMind spotted at a black barber shop, doxxed.
@Twig @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
image.png
@Twig @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
image.png
@Godsend @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
This is a horrific song, a stark horror!
This is a horrific song, a stark horror!
@DiamondMind @Godsend @bigmattoidchimpin @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Demon, still the same… 😛
video_1754449749653.mp4
Demon, still the same… 😛
video_1754449749653.mp4
Godsend
Godsend@annihilation.social
Aussie assassin droids incoming….
Fully equipped with Laser boomerangs.
@Twig @DiamondMind @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
image.png
Fully equipped with Laser boomerangs.
@Twig @DiamondMind @7666 @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
image.png
@Godsend @7666 @DiamondMind @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @sicp @stelo
Djokovic needs this one😆
Djokovic needs this one😆
horntoise
koropokkur@eveningzoo.club
wtf?! that sorority girl has a dark tan. pretty sure they didnt let negress girls into sororities in the 80s.
@koropokkur @Godsend @bigmattoidchimpin @dcc @7666 @f0x @fknretardlol @phnt @DiamondMind @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Got you, triggering every liberal😄
Got you, triggering every liberal😄
Godsend
Godsend@annihilation.social
@koropokkur World's changing @Twig @bigmattoidchimpin @dcc @7666 @f0x @fknretardlol @phnt @DiamondMind @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
@Godsend @koropokkur @7666 @DiamondMind @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @meso @mint @p @phnt @sicp @stelo
Indeed, purple dildo appears at a WNBA game
Indeed, purple dildo appears at a WNBA game
Ice fren
DrBtc@nicecrew.digital
Tans are out. Its just sun damage and you'll look like a dryed out piece of leather when you age. Preserve you're WHiteness
@koropokkur @Godsend @bigmattoidchimpin @dcc @7666 @f0x @fknretardlol @phnt @DiamondMind @dsm @p @sicp @stelo @ins0mniak @meso @mint @NeoCat @Leyonhjelm
Too many colors😆
Fix it, three colors
IMG_6171.jpeg
Too many colors😆
Fix it, three colors
IMG_6171.jpeg
@Godsend @7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
Great job, downloaded..
We start with a huge discovery, Barak Hessian Obama!
ssstwitter.com_1754739097559.mp4
Great job, downloaded..
We start with a huge discovery, Barak Hessian Obama!
ssstwitter.com_1754739097559.mp4
Godsend
Godsend@annihilation.social
@Twig need to do this to a collage of johnny’s most memorable scenes @7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
Edited 7 months ago
@Godsend @7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
You sent me the perfect song for Jonny, he could be a star someday😆
clideo_editor_af22fdc87fe94e668e91fb13c836301f.mp4
You sent me the perfect song for Jonny, he could be a star someday😆
clideo_editor_af22fdc87fe94e668e91fb13c836301f.mp4
Godsend
Godsend@annihilation.social
@Twig
It's #WhitePeopleWednesday , but alas! I ran out of white things to celebrate, you guys can do that.
Instead I would like to share with you a short story about one of the most well know rap songs of all time, and it is about 30 years old.
I remember as a kid thinking the dialogue was staged, turns out it was actual dialog held in the studio as this song was done...in...one..take!!??!! Mind blown!
Nas is truly one of the greatest.
@7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
How Nas Made a Classic in Just One Take 😳🔥 #90shiphop #rap.mp4
Nas - N.Y. State of Mind (Lyrics).mp4
It's #WhitePeopleWednesday , but alas! I ran out of white things to celebrate, you guys can do that.
Instead I would like to share with you a short story about one of the most well know rap songs of all time, and it is about 30 years old.
I remember as a kid thinking the dialogue was staged, turns out it was actual dialog held in the studio as this song was done...in...one..take!!??!! Mind blown!
Nas is truly one of the greatest.
@7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
How Nas Made a Classic in Just One Take 😳🔥 #90shiphop #rap.mp4
Nas - N.Y. State of Mind (Lyrics).mp4
@Godsend @7666 @DiamondMind @DrBtc @Leyonhjelm @NeoCat @bigmattoidchimpin @dcc @dsm @f0x @fknretardlol @ins0mniak @koropokkur @meso @mint @p @phnt @stelo
Excellent selection, a lengthy song, the chorus kicks in after 2minutes…. 😮
👇
clideo_editor_5204fd23b1054451a4197870e9adcce1.mp4
Excellent selection, a lengthy song, the chorus kicks in after 2minutes…. 😮
👇
clideo_editor_5204fd23b1054451a4197870e9adcce1.mp4
Dr. Coyote Owens, Conspiracy Therapist
Coyote@shitposter.world
Edited 7 months ago
@Godsend @Twig @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Leyonhjelm
Hrm.. apollogies, your post reached "dark fedi"... Most here will remove you from replys at your request. I have for this one, as to not bother.. And just remind others to do so. Untag _NeoCat_sacred.harpy.faith
Or did I just fall for a troll? I'm kinda high right now?
Hrm.. apollogies, your post reached "dark fedi"... Most here will remove you from replys at your request. I have for this one, as to not bother.. And just remind others to do so. Untag _NeoCat_sacred.harpy.faith
Or did I just fall for a troll? I'm kinda high right now?
@coyote @Godsend @dcc @7666 @f0x @fknretardlol @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @mint @Coyote @Leyonhjelm
He is gay 😆😑👻😈
He is gay 😆😑👻😈
@koropokkur @Godsend @dcc @7666 @f0x @fknretardlol @phnt @dsm @p @sicp @stelo @ins0mniak @meso @coyote @mint @Coyote @Leyonhjelm
Lemmy?!
No Way!
Lemmy?!
No Way!
@fknretardlol @Godsend @dcc @7666 @f0x @koropokkur @phnt @dsm @p @sicp @stelo @ins0mniak @meso @coyote @mint @Coyote @Leyonhjelm
Correct Hon…😆😈
Correct Hon…😆😈



 specifically stated that customers would receive an email about it and I got nothing.
specifically stated that customers would receive an email about it and I got nothing.
























 🇷🇺
🇷🇺